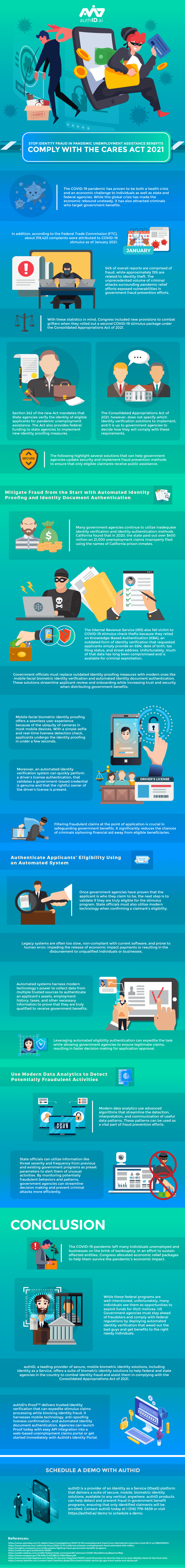
The coronavirus pandemic resulted inmore people ending up unemployed as their workplaces closed down. Because of this, more people needed government aid to get by as they unexpectedly lost their jobs.
Congress passed the Coronavirus Aid, Relief, and Economic Security Act to provide unemployment aid to eligible applicants, and state agencies were overwhelmed with the large number of enrollments. Many people applied to benefit from the CARES Act, including grifters that caused agencies to lose about 36 billion dollars collectively due to identity fraud.
The Federal Trade Commission reported that 319,423 complaints were made regarding the first rollout of the stimulus package. 54% of the stimulus complaints were about fraud, while 15% were identity theft.
To mitigate the risk of criminals stealing more money on the CARES Act’s second stimulus package rollout, Congress included new provisions focused on the state agencies verifying the applicant’s identity. The new provisions do not specify how the agencies must verify people’s identity, but using device-based authentication and biometric identity verification solutions are ideal.
Using biometric and device-based identity proofingcan help with the verification process while eliminating the risk of fraudsters getting verified. However, using such solutions requires the agencies to switch over from their aging KBA or knowledge-based authentication systems reliant on an individual’s SSN, date of birth, address, and tax filing status. Such information can easily be accessed by hackers and used for fraud, which is likely how the government lost 36 billion in the first place.
After replacing the KBA systems, state agencies must use modern data analytics to streamline the new system’s detection, interpretation, and communication process of useful data patterns. Data analytics are instrumental in helping government agencies combat fraud.
Government agencies must stop using legacy systems that hackers and fraudsters exploit for their own benefit and use newer solutions. For more information, check this infographic by authID.ai